Product Center
4009-610-038
Contact Us
Location:Home > Product Center >Detection of defensive >
To help companies deal with the current development of information technology such as web, cloud application of increasingly complex applications and security problem, letter day melts with the accumulation of more than 20 years of research and development of security and safety service experience, according to IDC, operators, the big universities such as flow type performance and security problems faced by the network environment, the day of the launch system based on NGTOS melting letter NGFW ? next generation firewall cheetah six series of products.

Deep recognition control
Letter day melt NGFW ? next generation firewall recognition engine of the application of the integrated use of single package features identification, multiple packet recognition, statistical feature recognition and other fine-grained, deep application and
agreement in the form of identification, and adopts the model of multi-layer match with multistage filtering architecture and encrypted traffic identification method based on patent, achieve accurate recognition of application layer protocols and applications.
At the same time, the day melt letter NGFW ? next generation firewall support depth of content filtering, read through the network protocol to the variety of the content analysis, from an exact match of keywords to content fuzzy search, from based on
file content to detection on the basis of file attributes, from passive to active events reported to intercept, a full range of data security protection measures can truly help enterprises to realize the network data security.
Flood, TCP SYN Flood, etc.), applied DDOS attacks (e.g., CC, DNS Flood, run out of slow connection, etc.), DOS attacks (e.g., Land, Teardrop, Smurf, etc.) attack, illegal agreement (such as IP flow, the TCP no tags, no confirm FIN, etc.) four categories of
denial of service attacks. Use a variety of defense mechanisms, through the flow of business early warning, proportional sampling analysis, source authentication, source of speed, step by step protocol analysis and pattern filtering, business application protection,
forced to protect a variety of technical means, such as precise and fast attack traffic block, safeguard user business network flow.
subnet for new connections, the number of simultaneous connections, flow data intelligent learning, forming a certain period of normal business baseline, comparative analysis and real-time data, alarm if it is abnormal. By linkage with APT sandbox, providing
virtual simulation running environment, according to the results of operation and the judgment for malicious code, and will be malicious characteristics analysis results (signature) uploaded to the firewall, the firewall to update the local dynamic characteristics of
the library, in order to deal with unknown malicious attacks, forming a "bypass serial dynamic real-time detection, blocking" linkage, reach the effect of active defense based on unknown threats.
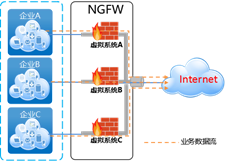
flow control, session management, application of recognition, virus defense, intrusion prevention, classification of WEB filtering, content filtering, audit reports a variety of functions such as virtualization. Mutual isolation between virtual system, can make the
system management, configuration management more convenient clear, and can avoid because of a virtual system failure or business busy wait for a reason and affect other virtual system.
Security visualization
Letter day melt NGFW ? next generation firewall with specialized supervisory control and data center function module, the administrator can quickly check equipment by monitoring the panel traffic statistics and comprehend the current running situation of the
equipment. According to interface, application, user, user group, servers, IPSec VPN check equipment flow statistics, check the equipment by the threat of information, check the equipment of IPv4 and IPv6 connection information, view the online user
information. Data center is mainly the security platform to realize the information statistics, including the summary of network events and archiving, data management and log to view, and according to the need to implement the report generation and data
export. In addition, the letter day melt NGFW ? next generation firewall internal audit system, to set user behavior, Internet traffic, online data on the length of the audit, such as web access to the situation in view of the relevant keywords, in view of the
fixed format data, file upload download behavior, etc., to help users from multiple angles, multi-dimensional understanding network usage.

广东大中信息技术有限公司 Powered by hunuo.com 粤ICP备18106562号-1
